6 Cybersecurity Tips for Remote Workers
Remote work opens the door to phishing, deepfake scams, and insecure home networks. Discover 6 essential cybersecurity tips every remote employee and IT team must follow to safeguard data, devices, and digital identities in a distributed workforce.
Ozan Ucar, Founder and CEO of Keepnet
Remote work is now a standard part of business, but cybersecurity for remote workers has become a critical concern. With employees logging in from home offices around the globe, organizations face new remote worker security risks – from AI-powered phishing emails to vulnerable home networks. In fact, 91% of cybersecurity professionals reported an increase in cyber attacks due to remote working (NIST cybersecurity guidance).
To help mitigate these threats, here are six remote work security tips for 2025. These work from home cybersecurity practices will keep both employees and IT administrators a step ahead of evolving threats, while subtly highlighting how Keepnet’s solutions support a secure remote workforce.
Keepnet: Mitigating Human Cybersecurity Risk in the Remote Workplace
Cybersecurity is a shared responsibility. Remote workers should remain vigilant and practice good cyber hygiene daily, while IT leaders must equip them with the right tools, training, and support.
When in doubt, remember that a culture of security awareness is one of the strongest assets a company can have. By fostering that culture and leveraging solutions like Keepnet’s security awareness training programs, phishing simulations, and incident response automation, businesses can empower their employees to identify and respond appropriately to threats. In the evolving landscape of cybersecurity for remote workers, staying one step ahead of attackers is challenging but achievable – and it starts with the essential tips outlined above. Stay safe, stay informed, and never stop learning, no matter where you work from.
Editor's Note: This article was updated on March 12, 2026.
1. Stay Vigilant Against AI‑Powered Phishing and Deepfake Scams
Cybercriminals are increasingly using artificial intelligence to supercharge their social engineering attacks. AI can craft thousands of highly convincing phishing emails in minutes, often personalized to each victim. This means a remote employee might receive a work from home security scam email that looks nearly identical to a legitimate message from their company.
Similarly, deepfake scams have emerged: attackers leverage AI to create fake audio or video that impersonates colleagues or executives. For example, even a major bank was duped out of $35 million by a cloned voice of a trusted client (Source) – a stark warning of how real this threat has become.
Tip: Treat any unexpected request with skepticism, especially those involving financial transactions or sensitive data.
If your “CEO” calls via voice message urgently asking for a transfer, verify through another channel because it could be an AI-generated impostor.
Organizations should conduct regular security awareness training to help staff recognize phishing clues and deepfake tricks. Simulated phishing exercises (like those offered by Keepnet’s Phishing Simulator) let remote employees practice spotting suspicious emails in a safe environment. A well-trained workforce is often the best defense against AI-enhanced attacks
By staying vigilant and verifying identities, remote workers can outsmart even the smartest phishing attempts. Implementing effective workforce password management ensures that employees maintain secure access credentials across all business systems
2. Secure Your Home Network and Smart Home Devices
When your home doubles as your office, your personal network’s security is just as important as the corporate network. Shockingly, an average home network faces 10 attempted cyber attacks per day (Netgear report).This is partly because today’s smart homes are filled with Internet-of-Things (IoT) devices – the average household has around 21 connected devices on the network.
Each device (from smart thermostats and speakers to work laptops and phones) is a potential entry point for hackers. Many IoT gadgets lack strong security out of the box: they often ship with weak default passwords, rarely receive updates, or communicate over insecure protocols.
If compromised, these devices can lead to privacy breaches or even provide a foothold to attack your work devices.
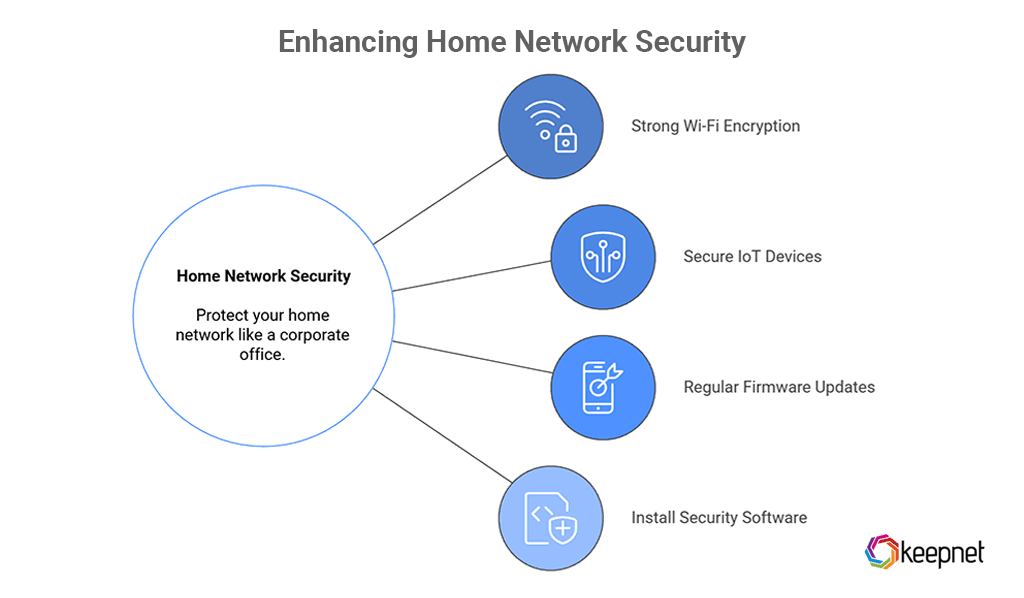
Tip: Treat your home like an extension of the corporate office. Some best practices to bolster your home network security include:
- Use a strong, encrypted Wi-Fi setup: Change default router passwords and use WPA3 encryption on your Wi-Fi network. This prevents eavesdropping or unauthorized access. Consider setting up a guest network for IoT devices so that your work computer is isolated from less-secure gadgets.
- Secure your IoT devices: Immediately change default credentials on any new “smart” device. Use strong, unique passwords (a password manager can help manage these). Enable multi-factor authentication on device apps whenever possible.
- Keep firmware updated: Regularly install updates for your router and IoT devices. Outdated firmware is a common weakness that attackers exploit.
- Install security software: If available, use home network security solutions (some routers offer built-in firewalls or malware blocking). At minimum, ensure your work devices have up-to-date antivirus/anti-malware protection.
Read our guide to learn more about how to protect your smart home.
By taking these steps, you significantly reduce the risk of outsiders infiltrating your home Wi-Fi or connected devices. This is a key work from home security best practice – maintaining a hardened home IT environment so it’s as secure as any office.
3. Implement Strong BYOD Policies and Device Protection
With the rise of remote and hybrid work, Bring Your Own Device (BYOD) is now the norm. Over 80% of organizations allow employees to use personal devices for work tasks.
While BYOD offers convenience and cost savings, it also introduces security challenges. Personal laptops, tablets, or smartphones might not have the same protections as corporate-issued devices. In fact, 22% of companies reported malware infections originating from employees’ own devices in the past year (Explodingtopics report).
Unmanaged devices could be missing critical patches or running insecure apps. Additionally, remote workers may connect to public or home Wi-Fi networks that are less secure – 22% of organizations found employees connecting to malicious Wi-Fi hotspots while working (Explodingtopics report).
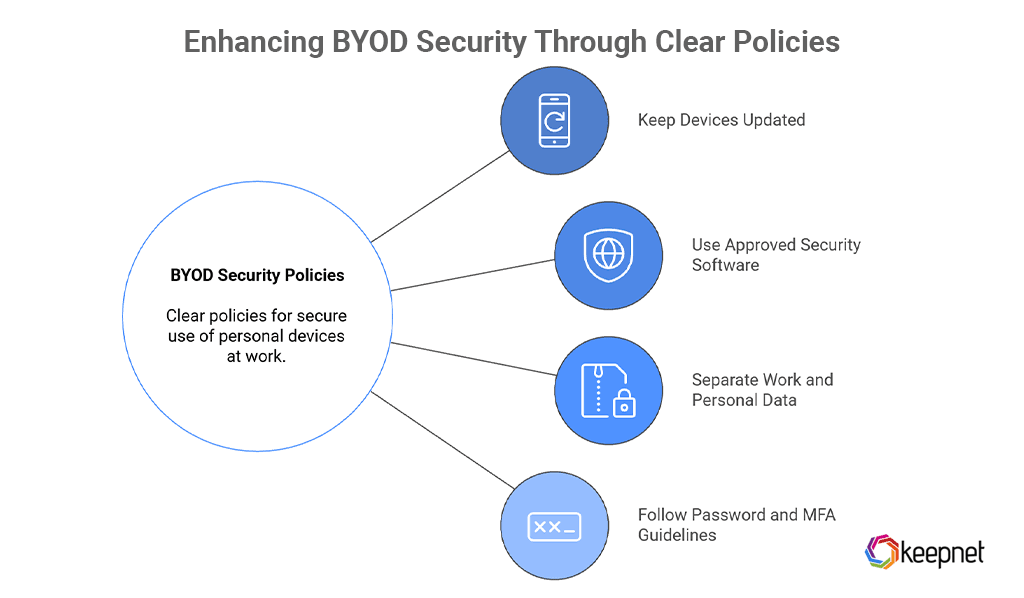
Tip: Companies and IT administrators must establish clear BYOD security policies, and employees should adhere to them diligently:
- Keep devices updated: Ensure your personal devices used for work have the latest operating system and software updates. Regular patching closes known vulnerabilities.
- Use approved security software: Install company-recommended endpoint protection (anti-malware, firewalls, mobile device management profiles) on your personal device. This helps detect threats and enforce security settings. For mobile devices, enabling remote wipe and locator functions is critical in case a device is lost.
- Separate work and personal data: Avoid mixing personal apps and work data on the same device if possible. Use a secure company-provided container or app for work email and files. This segmentation reduces the chance of a personal app leak affecting corporate information.
- Follow password and MFA guidelines: Use strong passwords for device login and enable multi-factor authentication on all work applications. Never share work credentials between family or personal services.
Both employees and employers share responsibility here. Remote workers should treat their own device with the same caution as a work computer, and organizations should provide tools (like VPNs, secure access gateways, or mobile security suites) to help protect BYOD usage.
By tightening device security and following work from home cybersecurity guidelines, the convenience of BYOD doesn’t have to come at the expense of security.
4. Adopt a Zero Trust Approach for Remote Access
Traditional perimeter security (where anyone inside the office network is trusted) no longer suffices when your workforce is distributed across homes and cafes.
In 2025, hybrid-cloud attacks and account breaches are on the rise as hackers target cloud services and remote access points. A stolen VPN credential or a misconfigured cloud app can be a gateway to your entire enterprise.
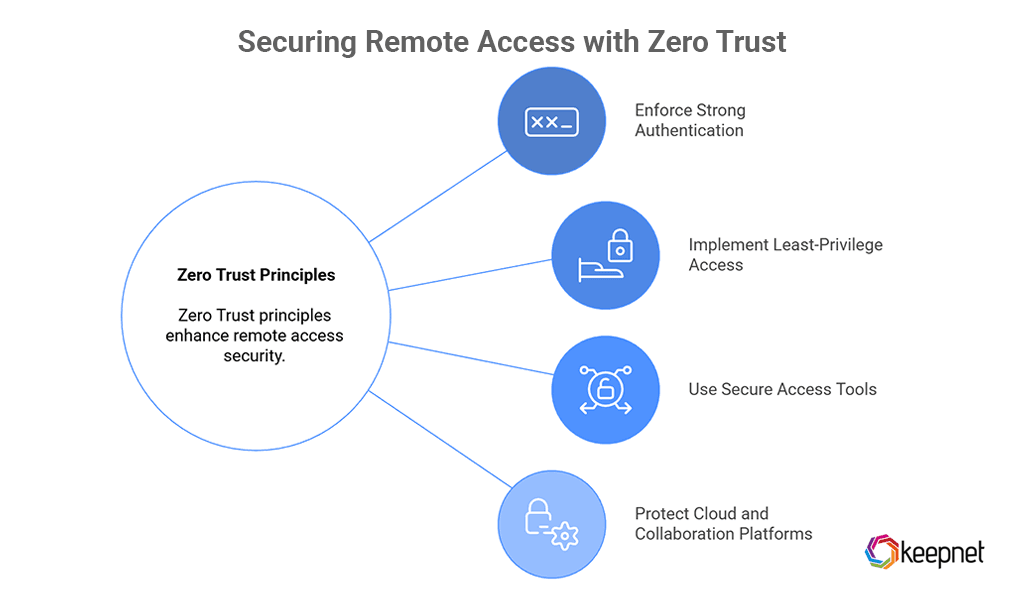
That’s why “Zero Trust” has become a cybersecurity cornerstone for remote work. Zero Trust means trusting nothing and verifying everything – every login, every device, every access request. Even if an attacker slips past one defense, additional checks can stop them from moving freely. As remote work and cloud services expand the corporate attack surface, zero-trust architectures ensure every access request is authenticated and authorized, no matter where it originates.
Tip: Embrace Zero Trust principles to secure remote access to company resources:
- Enforce strong authentication: Require multi-factor authentication for all remote logins and cloud applications. This alone mitigates the risk of stolen passwords being used. Modern phishing-resistant methods (like hardware security keys or biometrics) add even more protection.
- Implement least-privilege access: Remote employees should only have access to the data and systems necessary for their role. Limit admin privileges on endpoints. This way, even if an account is compromised, the damage is contained.
- Use secure access tools: Instead of relying solely on VPNs, organizations are deploying Zero Trust Network Access (ZTNA) solutions that evaluate the user’s identity and device health each time they connect. Ensure remote devices meet security standards (up-to-date patches, running approved security software) before granting access to sensitive systems. To further enhance security and maintain reliable, location-specific connections, many businesses are also adopting secure residential proxies, as they help mask IP addresses while ensuring that access appears legitimate and trusted, reducing the risk of blocking or unauthorized access.
- Protect cloud and collaboration platforms: Cloud apps used by remote teams (email, file sharing, project management) should have proper security configurations – like data leak prevention rules, login anomaly detection, and strict sharing permissions. Regularly review these settings to align with work from home security best practices.
Adopting Zero Trust does not happen overnight, but even incremental steps (like MFA and network segmentation) greatly strengthen remote work security. Notably, over half of organizations worldwide have already implemented or are planning to implement Zero Trust strategies by 2024 (Verizon report).
This trend reflects the reality that cybersecurity for remote workers must center on robust identity and access management. By eliminating implicit trust, companies can significantly reduce the risk of breaches via compromised remote accounts or devices.
Read our article to learn more about zero trust architecture.
5. Maintain Ongoing Security Awareness Training
Technology alone cannot stop all attacks – people play a crucial role. Studies show that human error is involved in the majority of breaches (68% of data breaches in 2024 involved mistakes like falling for phishing scams).
Remote employees, often isolated from on-site IT support, need regular training to stay alert against ever-evolving threats. Security awareness training shouldn’t be a one-off annual checkbox, but a continuous program that keeps cybersecurity top-of-mind. In a home setting, employees may be more prone to click a phishing link or use bad security habits if not reminded otherwise. Regular training combats complacency by updating staff on new scam techniques (for example, an AI-generated “Zoom meeting” invite that is actually a phishing link) and reinforcing best practices.
Tip: Organizations should invest in engaging, up-to-date security awareness training programs tailored for remote work scenarios.
Keepnet’s Security Awareness Training platform, for instance, provides interactive modules and even AI-driven phishing simulations to educate employees in real-world threat scenarios.
By running periodic phishing simulation campaigns (covering email, SMS, even voice phishing), employees can practice spotting and reporting suspicious messages in a safe environment. This kind of hands-on training has been shown to boost phishing detection rates significantly. It also helps identify which employees or departments might need extra coaching.
Additionally, create a security-conscious culture: encourage remote staff to share any unusual emails or incidents they encounter, and celebrate those who do report threats. Gamify the training experience with quizzes or rewards to keep engagement high despite the distance.
The goal is to ensure every remote worker feels responsible for cybersecurity and confident in applying remote work security tips daily – from spotting a dubious link to using a secure password manager. With well-informed people, the chances of a cyber incident plummet.
6. Stay Compliant and Prepare for Remote Incidents
The cybersecurity landscape is not only shaped by criminals, but also by regulators. Governments and industry bodies worldwide have introduced stricter work from home security best practices and regulations in response to the remote work boom.
For example, the EU’s recent NIS 2 Directive (enforced in late 2024) mandates that organizations in critical sectors implement measures like incident reporting and cybersecurity training (Schellman report). This means companies could face penalties if they don’t ensure remote employees are trained or if they fail to report a serious security incident within a given timeframe.
Other laws (such as the Digital Operational Resilience Act for financial firms, or various data protection regulations) similarly require businesses to maintain robust cyber defenses and incident response capabilities, regardless of where employees are working. Compliance, therefore, has become a driving force for improving remote security standards.
Tip: Both enterprises and remote workers must prioritize compliance and incident preparedness. Make sure you follow your organization’s security policies to the letter – these rules exist not just for security’s sake, but often to meet legal requirements.
From using approved cloud storage for work files (to comply with data privacy laws) to encrypting sensitive data and emails, adhering to policies helps keep the company compliant and your data safe.
Equally important is having a clear plan for incident response that extends to the home office. Remote workers should know exactly how to report a security incident or suspected breach.
If you click on a phishing email or lose a company device, time is of the essence. Companies are advised to implement easy reporting channels (like a one-click phishing report button or a hotline) and leverage incident response automation tools to react quickly. For instance, automating phishing incident response can speed up email threat analysis dramatically – by up to 165 times faster than manual analysis.
Keepnet’s Incident Response module is one example that can automatically analyze reported phishing emails, quarantine malicious messages across all inboxes, and even share threat intelligence broadly to stop the same attack from spreading. This kind of rapid containment is crucial when IT teams cannot physically assist an employee in person.
By preparing for the worst (having backups, response playbooks, and automated tools in place), organizations ensure that even if a remote security breach occurs, it can be swiftly managed with minimal damage. In sum, staying compliant with evolving regulations and ready to respond to incidents are twin pillars of remote work security. They underscore to employees and regulators alike that the company is serious about protecting data in every work environment.
Remote work is here to stay, and so are the cyber threats targeting distributed teams. The remote worker security risks of 2025 – from AI-driven phishing and deepfakes to IoT-based attacks – require a proactive and layered defense. By following these six remote work security tips and work from home security best practices, organizations and their employees can significantly reduce the likelihood of a costly breach. Key takeaways include staying alert to new forms of social engineering, locking down home networks and personal devices, embracing Zero Trust principles, and continuously educating the workforce.
Remote Work Rules That Actually Hold Up
Remote work security breaks down when guidance is too broad to use. Employees do better with a few clear rules they can apply during normal work, especially when they are moving between home networks, personal devices, cloud apps, and urgent collaboration requests.
The strongest advice is practical and repeatable. It should help people verify requests, protect access, and know how to report suspicious activity without slowing work to a halt.
Keepnet teams usually see stronger results when content like this is tied to a clear workflow, owner, and reporting path. A common mistake is treating 6 cybersecurity tips for remote workers as background knowledge instead of a decision that shows up in real operations.
Remote Work Checklist
- Use approved devices and keep identity and VPN controls current.
- Verify unusual requests in a second channel before sending data or approving changes.
- Separate work accounts from personal email, storage, and messaging where possible.
- Report suspicious prompts, files, and login alerts as soon as they appear.