Adversary in the Middle (AiTM) Phishing: How to Detect, Prevent, and Protect Your Business in 2026
AiTM phishing bypasses traditional MFA and leads to account takeover, session theft, and business email compromise. Learn how it works, how to detect it, and how to reduce the risk.
AdversaryintheMiddle (AiTM) phishing is the natural evolution of the classic ManintheMiddle (MitM) attack. It uses reverse proxies and phishingasaservice kits to steal credentials, session cookies, and live access at scale. In a typical AiTM campaign, the attacker places a malicious proxy between the victim’s browser and a legitimate service such as Microsoft 365, Google Workspace, or Okta. The victim sees a normal login flow. The attacker captures the credentials and the live session at the same time.
Why does this matter in 2026? Because AiTM weakens the controls many teams trust most, including MFA, passkeys, and device based checks. The attacker does not need to break those controls directly. Instead, they steal the proof of authentication after the user completes it. Once inside, adversaries can bypass conditional access policies, manipulate email flows, and launch BEC attacks from inside trusted inboxes.
The trend is accelerating in 2026. Veriff's 2025 Identity Fraud Report recorded a 46% year over year rise in AiTM incidents across high value sectors such as finance and healthcare. Researchers have also demonstrated how attackers abuse QR code fallback flows in passkey deployments, which means even phishing resistant configurations are no longer guaranteed safe.
Bottom line: If your security roadmap does not explicitly address Adversary in the Middle phishing, it is already behind the current threat landscape.
How AdversaryintheMiddle (AiTM) Phishing Works
Unlike classic phishing, AiTM weaponizes your own successful MFA flow against you, stealing the proof of authentication rather than guessing or brute forcing it.
StepbyStep Mechanics of an AiTM Attack
Understanding the stepbystep mechanics of an AIDriven attack is important for developing effective defenses and protecting sensitive information:
- The lure: Victims receive a persuasive email, SMS, or socialmedia DM that masquerades as a routine “Signin required” notification. A cleverly crafted URL hides a reverseproxy domain such as m365loginsecure[.]com.
- Transparent reverse proxy spins up: Tools like EvilProxy, Tycoon 2FA, Sneaky 2FA or opensource kits (Evilginx, Modlishka) stand between the victim’s browser and the legitimate service (e.g., Microsoft 365). The HTTPS certificate is real, so the lock icon offers no comfort.  
- Credential harvesting & realtime relay: The user types a username and password into a pixelperfect facsimile of the real page. The proxy forwards those credentials upstream so the service behaves normally, while storing a local copy for the attacker. 
- MFA interception/replay: When the service issues an MFA challenge (TOTP, push, WebAuthn, even FIDO passkey QR fallback), the proxy relays it instantly. The victim resolves the prompt, believing it legitimate, and the proxy siphons off the resulting session cookie or OAuth token. 
- Session hijack & persistence: Armed with a live, fully authenticated session, the attacker scripts API calls or logs in through headless browsers, bypassing Conditional Access and geofencing. They may set up additional app passwords, register new MFA devices, or drop malicious OAuth apps to persist. 
- Postcompromise operations: Common next steps include BusinessEmailCompromise wirefraud templates, dataexfiltration from cloud drives, and lateral movement into SaaS admin portals.
Real World Scenario: Operation Sneaky Invoice
Imagine your CFO finishing a late flight checkin. An email marked Urgent: invoice approval lands in her inbox. She taps the link, sees Microsoft 365’s familiar login, enters credentials, and approves her push notification. Within 40 seconds attackersrunning the Sneaky 2FA PhaaS kit identified in early 2025have cloned her session cookie, created a new Outlook rule that hides replies, and launched $1.3 million of wire requests to APAC suppliers before breakfast. The entire breach required no malware on the endpoint and no passwordreset linkjust a relay.  
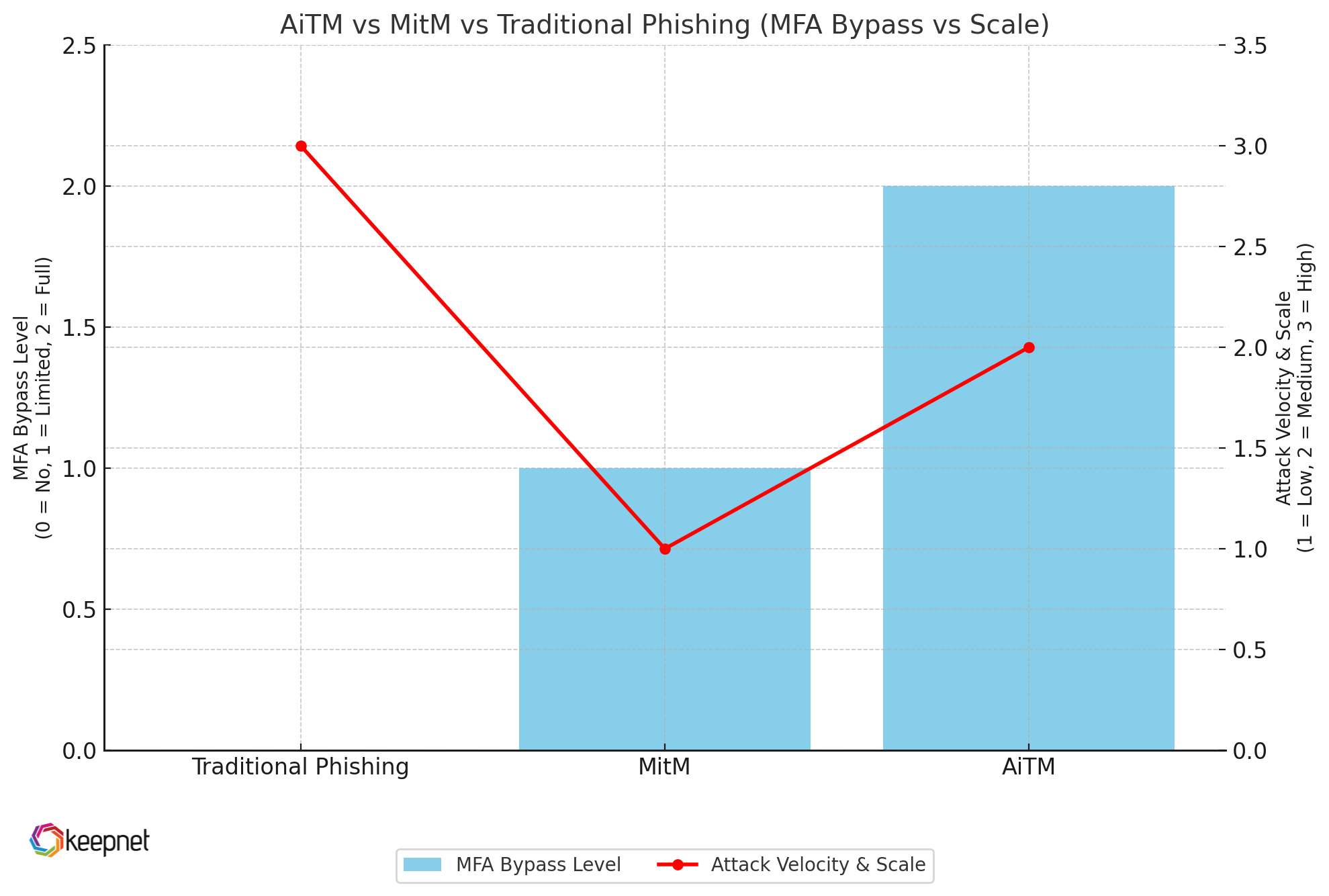
AiTM vs Classic MitM vs Spray and Pray Phishing
MitM attacks focus on intercepting raw traffic at the network layer; AiTM proxies the application layer, giving it surgical access to authentication flows.
| Attack Vector | MFA Bypass Capability | Attack Velocity & Scale |
|---|---|---|
| Traditional credential phishing | No stops at password | Very high (massscale via email/SMS) |
| ManintheMiddle (MitM) | Limited SSL stripping or cert abuse needed | Low (requires LAN or physical proximity) |
| AdversaryintheMiddle (AiTM) | Yes token & cookie theft after MFA | High (cloudbased kits, PhaaS dashboards) |
Table 1: AiTM vs MitM vs Traditional Phishing
AiTM phishing collapses the security stack by turning your own successful MFA handshake into an access token. If your roadmap stops at enabling MFA, you are defending yesterday's threat landscape.
Types of AdversaryintheMiddle (AiTM) Phishing Attacks
AiTM is not a single technique. It is a family of tactics that abuse the authentication flows designed to protect users. Below are four patterns security leaders should track closely.
CredentialHarvesting AiTM Attacks
Credentialharvesting AiTM attacks work using a cloudhosted reverse proxy (EvilProxy, Tycoon 2FA, Sneaky 2FA) that clones a Microsoft 365 or Google Workspace login page pixelforpixel. The victim’s username and password are streamed to the attacker while being forwarded upstream so the real service accepts them without error.
- Why it is lethal: Automation built into Phishing as a Service (PhaaS) kits lets operators stand up thousands of fake tenants, rotate domains, and refresh TLS certs daily. PhaaS growth continues to accelerate into 2026.
Session Hijacking AiTM Attacks
Instead of storing passwords for later use, the proxy steals the session cookie or OAuth token generated after MFA. Attackers replay it through a headless browser or the Microsoft Graph API, materializing inside the inbox within seconds.
- Real world proof: Tycoon 2FA continued adding browser fingerprinting evasion and encrypted payload delivery specifically to protect stolen session cookies from detection tooling. In 2026 this pattern is now standard across leading PhaaS platforms.
MFA Interception & Replay AiTM Attacks
The proxy relays push approvals, TOTP codes, or WebAuthn challenges in real time. Because the victim completes MFA, the attacker does too. Nothing is broken, it is simply duplicated.
- 2026 snapshot: Researchers observed broad campaigns in which AiTM operators harvested more than 500,000 fresh MFA tokens in under three weeks, fueled by subscription PhaaS dashboards that show live MFA pass rates to paying affiliates.
QRCodeBased AiTM Phishing
Modern passkeys and some hardware FIDO keys allow a crossdevice signin fallback: scan a QR code on one device to approve on another. AiTM proxies exploit this workflow by surfacing a bogus QR code that the victim dutifully scans, handing over a fresh FIDO assertion in the process.
- 2026 update: The PoisonSeed campaign demonstrated attackers bypassing FIDO keys at scale using spoofed portals that forced QR fallback flows, prompting Microsoft and Okta to update guidance on disabling cross device authentication.
Key Takeaways for 2026
- Credential harvesting is no longer the end game. Session hijack is the primary objective.
- MFA interception proves that MFA enabled is not the same as MFA safe.
- QR code phishing now defeats even hardware FIDO keys when fallback flows are not disabled.
- PhaaS platforms commodify all four AiTM variants, making them accessible to low skill attackers.
If your security roadmap does not explicitly test, monitor, and block all four AiTM variants, you are leaving a gap that modern adversaries are already exploiting in 2026.
Comprehensive Report on RealLife AiTM Phishing Incidents ( Case Studies)
AdversaryintheMiddle phishing attacks represent a sophisticated evolution of traditional phishing, where attackers intercept communications between users and legitimate services to steal credentials, session cookies, and other sensitive data. These attacks are particularly dangerous because they can bypass multifactor authentication, a security measure many organizations rely on. Below is a detailed analysis of prominent realworld AiTM phishing incidents from recent news, including case studies, lessons learned, and mitigation strategies, supported by reputable sources.
Darktrace Case Study: DropboxBased AiTM BEC Attack (October 2024)
A multistage AiTM Business Email Compromise (BEC) attack leveraged Dropbox to deliver phishing links. Attackers targeted lowerpriority users, exploiting Dropbox’s trusted reputation to encourage users to click malicious links embedded in emails with subject lines like “FirstLast shared ‘Filename’ with you.” Techniques included session cookie theft and MFA bypass, with suspicious activities such as logins from rare geolocations (e.g., Kenya, IP 41.90.175.46) and registration of new MFA methods via Microsoft Authenticator.
- Detection and Mitigation: Darktrace’s AIdriven security platform identified anomalous login patterns and MFA changes, escalating the issue to their Security Operations Center (SOC). Autonomous response mechanisms disabled the compromised SaaS account, preventing data exfiltration. The customer was notified to reset passwords and implement remedial actions.
- Lessons Learned: Trusted cloud services like Dropbox are prime targets for AiTM attacks due to their widespread use and perceived legitimacy. Realtime monitoring for unusual login locations and MFA changes is critical for early detection. Autonomous response systems can effectively contain attacks by quickly disabling compromised accounts.
Microsoft Security Blog: Banking Sector AiTM and BEC Campaign (June 2023)
A multistage AiTM phishing and BEC campaign targeted banking and financial services organizations, originating from a compromised trusted vendor. The threat actor, tracked as Storm1167, used an indirect proxy instead of a reverse proxy, providing greater control and flexibility in phishing page design. Attackers stole session cookies to bypass MFA, performed session replay attacks, and modified MFA methods without challenge, including adding a OneWaySMS method with an Iranian phone number. The campaign sent over 16,000 emails in a secondstage phishing effort, using unique sevendigit codes in email subjects to track targets.
- Detection and Mitigation: Microsoft’s detection alerts identified stolen session cookies, possible AiTM attempts, suspicious inbox manipulation rules, and anomalous tokens. Mitigation actions included revoking session cookies, rolling back MFA modifications, and requiring MFA rechallenges for updates.
- Lessons Learned: Compromised trusted vendors can serve as entry points for sophisticated AiTM attacks. Indirect proxies enhance attackers’ ability to customize phishing campaigns. Comprehensive monitoring and rapid response to detection alerts are essential to limit damage.
Proofpoint Case Study: Tycoon 2FA PhaaS Attack on Microsoft 365 (April 2025)
A largescale AiTM phishing attack targeted thousands of organizations worldwide using the Tycoon 2FA PhishingasaService (PhaaS) platform. The attack mimicked Microsoft 365 authentication screens, customized with the target organization’s Entra ID (formerly Azure Active Directory) branding. Attackers stole usernames, passwords, 2FA tokens, and session cookies, using advanced evasion tactics like invisible Unicode characters, custom CAPTCHAs, and antidebugging features.
- Detection and Mitigation: Proofpoint’s Nexus AI platform detected the threat by identifying suspicious URL domains, uncommon senders, precisionvalidated phishing, reverse proxy techniques, and custom branding on phishing pages. The attack was detected within customer data, even behind defenses of six other email security vendors, three of which are leaders in the 2024 Gartner Magic Quadrant for Email Security Platforms. Recommended protections include enhanced authentication (e.g., FIDO2 hardware tokens), user education, improved email filtering, and advanced threat detection systems like Proofpoint’s Account Takeover Protection (ATO) and Targeted Attack Protection (TAP)
- Lessons Learned: PhaaS platforms like Tycoon 2FA enable attackers to launch sophisticated AiTM campaigns at scale. Custombranded phishing pages increase the likelihood of deceiving users. Multilayered defenses, including advanced authentication and user training, are critical to counter such threats.
Zscaler Case Study: GmailTargeted AiTM Attack (July 2022)
An AiTM phishing attack targeted enterprise users of G Suite (Gmail), specifically chief executives, senior members, and their assistants in the US. The same threat actor behind a previous Microsofttargeted campaign used similar tactics, techniques, and procedures (TTPs), with infrastructure overlap (e.g., loftds[.]com redirector)
Phishing emails impersonated Google, posing as passwordexpiry reminders to prompt users to click malicious links.
The attack chain involved multiple URL redirections, Open Redirect abuse of Google Ads and Snapchat, and clientside fingerprinting to evade automated analysis systems. The attack bypassed Gmail’s MFA using proxybased phishing kits.
- Detection and Mitigation: Zscaler detected the attack, identifying indicators like HTML.Phish.Gmail. Users were advised to verify URLs before entering credentials to prevent falling victim to such attacks.
- Lessons Learned: AiTM attacks are not limited to Microsoft services; other platforms like Gmail are also vulnerable. Senior executives are prime targets for BEC due to their access to sensitive data and authority. MFA alone is insufficient; user vigilance in verifying URLs is important.
Technical Breakdown: Behind the Scenes of an AiTM Attack
To truly defend against AdversaryintheMiddle phishing, we need to dissect how these attacks are engineered from the ground up. From domain spoofing to token replay automation, modern AiTM campaigns operate like professional SaaS products, complete with dashboards, live metrics, and modular toolchains. This section unveils the technical anatomy of a fullblown AiTM operation.
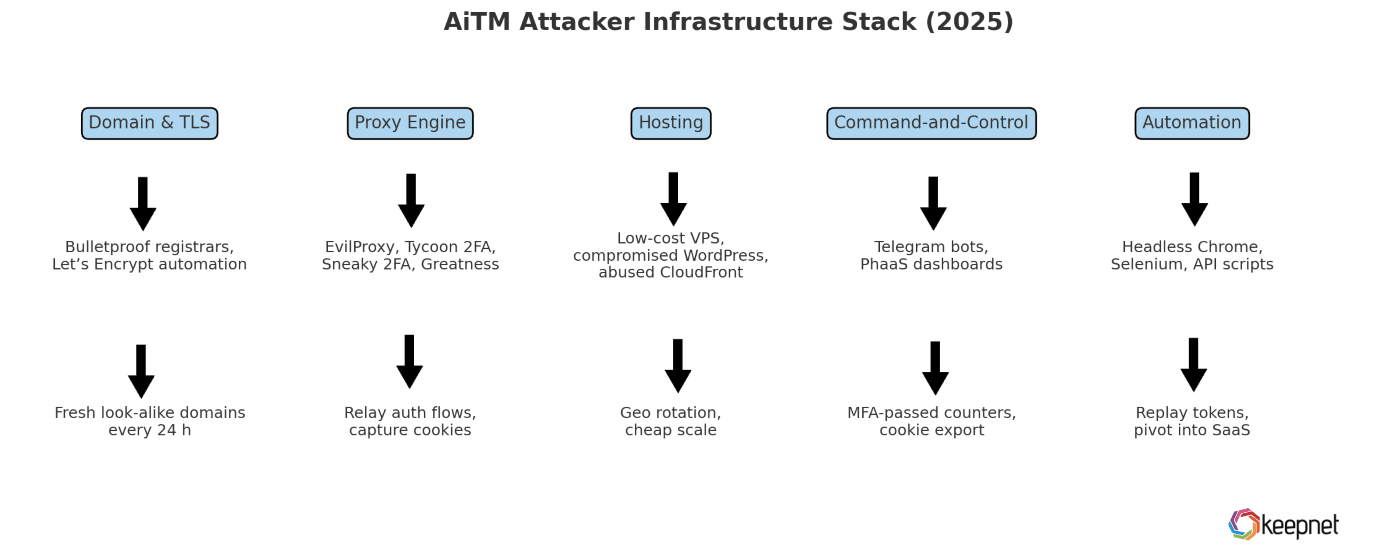
Attacker Infrastructure in 2026
In 2026, AiTM attackers operate with the precision and scalability of cloud native engineering teams. Their infrastructure is modular, automated, and built to bypass MFA at scale. Below is a breakdown of each core layer in the AiTM tech stack and the tools that power modern campaigns.
| Layer | Typical Tools & Services | Purpose |
|---|---|---|
| Domain & TLS | Bulletproof registrars, Let’s Encrypt automation | Fresh lookalike domains every 24 h |
| Proxy Engine | EvilProxy, Tycoon 2FA, Sneaky 2FA, Greatness | Reverseproxy that relays auth flow and captures cookies |
| Hosting | Lowcost VPS, compromised WordPress sites, or CloudFront abused via freetier | Geographic rotation + cheap scale |
| CommandandControl | Telegram bots, SaaS dashboards (PhaaS) | Live “MFApassed” counters, stolen cookie export |
| Automation | Headless Chrome + Selenium / Graph API scripts | Replays tokens, deploys mailbox rules, pivots to SaaS |
Table 2: Attacker Infrastructure in 2025
Barracuda saw >1 million PhaaS-powered AiTM attacks in just January–February 2025.
Inside a Modern AiTM Phishing Kit (Example: Tycoon 2FA)
Modern AiTM kits look more like SaaS products than oneoff phishing pages. They package dashboards, automation, and credential capture into a reusable service. Here’s what operators typically get:
- Prebuilt whitelabel portals: Spin up fake login flows for Microsoft 365, Google Workspace, Okta, or Zscaler with a checkbox. Pages are dynamically pulled from the real service to ensure pixelperfect cloning.
- Oneclick domain and TLS provisioning: The kit autogenerates subdomains (e.g. loginauthportal[.]com) and immediately attaches valid SSL certificates via Let’s Encryptno manual setup required.
- Live campaign dashboards: See realtime counters like “MFA passed” and “Credentials harvested” for each target, helping operators track ROI and tweak lures.
- Session cookie exfiltration API: Each time a victim completes MFA, the kit pushes the active session token to a Telegram bot or webhookready to be replayed within seconds.
- Persistent foothold tools: With a single toggle, the attacker can silently register rogue OAuth apps or enroll a new MFA method on the victim’s account for longterm access, even if the password changes.
Bottom line: Tycoon 2FA does not just phish credentials. It commodifies full session hijack with automation pipelines. If your SOC only watches for login failures or password reuse, this attack slips right past your defenses.
EndtoEnd Flow
To understand how AdversaryintheMiddle phishing unfolds in real time, it helps to zoom out and see the full attack chain, from the first click to complete session takeover. The diagram below visualizes each phase of the AiTM flow, showing how attackers intercept credentials, bypass MFA, and hijack sessions with surgical precision, all without triggering traditional alarms.
- Link click: Victim lands on proxy.
- Credential relay: Proxy forwards username/password, records copy.
- MFA relay: Victim approves push/TOTP/QR; proxy captures assertion.
- Cookie theft: Auth token exfiltrated to attacker.
- Postlogin abuse: Scripts use token to exfil data, set mailbox rules, launch BEC.
Key Technical Insights for Defenders
- Bind your tokens to the device: Session hijacking starts where MFA ends. Enforce devicebound tokens and enable Continuous Access Evaluation (CAE) to instantly revoke access when cookies are compromised.
- Fuse telemetry across layers: Connect the dots between email gateway URL rewrites and IdP signin logs. If a link click is followed by an MFA success from a new IP within secondssound the alarm. That’s an AiTM fingerprint.
- Fingerprint the proxy: Many AiTM phishing kits leave behind telltale signs in their TLS JA3 hashes or SNI values. Feed these into your firewall, secure web gateway, or XDR for proactive blocking.
If your detection logic stops at “MFA passed,” you’re already too late. AiTM lives in the post-MFA world, and unless you’re monitoring for token integrity, you’re handing attackers a valid key to your front door.
Indicators of Compromise (IoCs)
AdversaryintheMiddle phishing doesn’t leave behind the usual broken login attempts or bruteforce trails. Instead, it slips through in silencerelying on stolen session tokens and live credential relays. Spotting an AiTM breach means looking for signals that normal behavior happened at the wrong time, from the wrong place, or with the wrong fingerprint.
- Behavioral IoCs to Watch For: Successful logins from new IPs immediately after email clicks, (especially if IP geolocation differs significantly from the user’s known location).
- MFA success from unrecognized devices: This is followed by highprivilege actions (forwarding rules, app password creation).
- Duplicate sessions: One user appears to be logged in from two locations simultaneouslyone real, one attackercontrolled.
- OAuth application grants: These weren’t userinitiated. Especially those with access to mail, calendar, or file APIs.
Technical Artifacts & NetworkLevel IoCs
JA3 hashes / TLS fingerprints: Certain AiTM kits reuse the same TLS stacks or SNI strings. Feed known bad fingerprints into your web proxy or firewall.
- Suspicious domain patterns:Common examples include subdomains like loginauth[.]xyz, secureo365[.]cloud, or mfaverify[.]site, often with recent registration dates and Let’s Encrypt TLS certs.
- Session cookie anomalies: Tokens used on different OS/browser/device combinations within short timeframes (session replay).
Pro tip for SOC teams: If your alert rules only fire on failed logins or brute force attempts, you’ll miss AiTM entirely. Update detection logic to correlate successful MFA events with recent URL click-throughs and new device fingerprints. That’s where AiTM lives.
Impact and Consequences of AiTM Phishing Attacks
Adversary in the Middle (AiTM) phishing attacks do not just result in stolen passwords. They bypass multi factor authentication, compromise live sessions, and escalate to full data breaches. The damage unfolds fast, and the ripple effects can last for months or years. Understanding the true impact is essential for justifying the investment in proactive defenses.
Organizations often underestimate these attacks because they appear to start as simple login events, but the consequences go far beyond the inbox.
ShortTerm vs. LongTerm Impacts
In the immediate aftermath of an AiTM breach, the focus tends to be on containment: isolating compromised accounts, revoking sessions, and notifying stakeholders. But the longterm damage can be far more difficult to quantify and recover from.
Shortterm impacts:
- Immediate loss of email and document access
- Internal communication breakdown due to mailbox rule manipulation
- Delayed detection leading to multiaccount lateral movement
Longterm consequences:
- Persistent access via OAuth apps or rogue MFA devices
- Regulatory fines due to delayed breach reporting
- Breakdown in customer trust and executive accountability
Financial, Reputational, and Legal Consequences
AiTM phishing attacks are among the costliest forms of social engineering, especially when they result in business email compromise (BEC) or intellectual property theft.
Financial risks include:
- Wire transfer fraud totaling millions of dollars
- Legal fees and forensic investigation costs
- Revenue disruption due to system lockouts
Reputational risks include:
- Loss of customer confidence and vendor trust
- Negative media coverage that affects brand perception
- Social media fallout from leaked internal emails
Legal risks include:
- Noncompliance with GDPR, CCPA, HIPAA, or sectorspecific mandates
- Classaction lawsuits from impacted customers or partners
- Boardlevel liability in the absence of adequate controls
If your organization still treats phishing as a basic threat, it is missing the real danger. AiTM phishing does not just compromise accounts. It erodes trust, drains capital, and leaves legal teams scrambling. Understanding the full impact is the first step toward prevention.
Advanced Detection Methods for AiTM Phishing
Traditional detection tools are built to catch brute force attempts, credential stuffing, and malware payloads, not attacks that happen after a successful login. Adversary in the Middle phishing thrives in the gaps between identity platforms, browsers, and behavioral analytics. To detect these stealthy attacks in 2026, security teams need layered visibility that extends beyond the authentication event itself.
AIDriven Threat Detection
Artificial intelligence has become a critical detection layer for AiTM activity in 2026. AI models can instantly process diverse signals including MFA location data, login frequency, device posture, and browser type to determine when a session looks suspicious even after authentication succeeds.
Key capabilities of AIbased AiTM detection systems include:
- Realtime analysis of login patterns and token usage
- Detection of simultaneous or rapidsequence logins from multiple geographies
- Behavioral deviation user risk scoring that flags risky sessions, even when MFA was passed
When paired with cloudnative identity providers, AI threat engines can isolate compromised sessions before attackers reach sensitive data.
BrowserLevel Detection Mechanisms
The browser is where AiTM phishing begins, and often, where it can be stopped. By integrating security controls directly inside the browser environment, organizations can detect when login flows are being intercepted or proxied.
Modern approaches include:
- CSP (Content Security Policy) violation reports that flag unauthorized domain calls
- Browser fingerprinting to detect inconsistencies between what the user expects and what the proxy serves
- WebAuthn telemetry, revealing if authentication was completed on a registered device or manipulated through fallback methods
These tools give security teams visibility not just into what users do, but how and where they do it. That context is critical for validating the legitimacy of a session in the post MFA world.
Behavioral Analytics and Anomaly Detection Tools
The final piece of the puzzle is understanding behavior over time. AiTM phishing often looks like normal user behavior in the moment. But zoomed out across hours or days, the anomalies emerge: a user logs in from Germany seconds after clicking an email in Canada; an OAuth grant is approved for a tool the user has never touched; a mailbox rule appears that forwards all email to a disposable address.
Behavioral analytics platforms build an identity graph that maps what each user’s digital life normally looks like, then flags events that break the pattern.
Capabilities worth implementing:
- Crossapp and crossdevice behavior mapping
- OAuth anomaly detection
- Identity risk scoring based on context and deviation from norm
In the post MFA world, the best detection strategy is not just about stopping logins. It is about monitoring what happens next. With AI, browser level visibility, and behavioral baselines, security teams can catch AiTM attacks in the act before damage is done.
Why AiTM Attacks Are Critical to the Success of Business Email Compromise (BEC)
Business Email Compromise has traditionally relied on social engineering tactics, impersonating executives, spoofing domains, and convincing finance teams to wire money. In 2026, those tactics have evolved significantly. Today's most successful BEC campaigns are powered by Adversary in the Middle (AiTM) phishing attacks that grant real, authenticated access to executive inboxes rather than just impersonating them.
If you are protecting against BEC without defending against AiTM, you are only fighting half the battle.
How AiTM Fuels Modern BEC Scenarios
AiTM phishing provides the perfect launchpad for BEC:
- Bypasses MFA completely: Once the attacker has the session token, they don’t need to steal the password again. MFA is rendered useless.
- Grants full inbox visibility: Attackers read internal email threads in realtime, understand payment schedules, vendor relationships, and communication styles.
- Sets up stealthy persistence: Through malicious mailbox rules or OAuth apps, the attacker can observe and manipulate conversations over days or even weeks without being detected.
- Launches from trusted infrastructure: Because the attacker sends emails from the real corporate account, there are no spoofing indicators or failed DMARC logs to trigger alarms.
Why Security Teams Must Align AiTM and BEC Defenses
- BEC is not just a human error anymore. It’s now a hybrid attack, using technical compromise (AiTM) to enable psychological manipulation (BEC).
- Email security gateways won’t catch this. There’s no spoofing, no strange domains, no external sender to block. Therefore, protect your secure email gateways (SEGs).
- MFA is not enough. If your BEC defense strategy starts and ends with “we have MFA enabled,” you are vulnerable to AiTM.
How to Prevent AdversaryintheMiddle Phishing
Stopping AdversaryintheMiddle (AiTM) phishing requires more than firewalls and MFA. These attacks succeed by exploiting human trust and technical blind spots, especially in the gaps between email security, identity platforms, and browser behavior. Prevention must be multilayered, combining user training, technical safeguards, and detection logic tailored to AiTM tactics.
Here is what prevention looks like in 2026.
Employee Training and Awareness Programs
Your employees are the first line of defense. AiTM phishing preys on urgency and realism, often imitating legitimate sign in portals with pixel perfect accuracy. Even well trained employees can be deceived, which is why human layer hardening must be continuous.
To harden your human layer using security awareness training:
- Include AiTMspecific scenarios in phishing simulations (e.g., MFA interception and QRbased lures)
- Train users to recognize suspicious login pages, especially those with unusual domains, generic branding, or QR phishing prompts
- Reinforce the importance of reporting any login prompt that feels “off”, even if it includes an MFA step
The moment staff understand that passing MFA does not always mean they are safe, your organization's defense posture improves significantly.
Technical Safeguards for Stopping AiTM Attacks
Even the best trained employees will occasionally fall for a well crafted lure. That is why your infrastructure needs controls designed specifically to prevent token theft and replay attacks.
Top technical safeguards include:
- Enforce phishingresistant MFA (WebAuthn, FIDO2) with device binding and no QR fallback
- Enable Continuous Access Evaluation (CAE) to revoke tokens in real time when conditions change
- Use secure DNS filtering to block known AiTM kit domains (e.g., EvilProxy, Tycoon 2FA, Greatness)
- Implement browser isolation or inspection tools to detect proxy manipulation at the endpoint
- Correlate email gateway click logs with IdP login telemetry to catch postMFA anomalies
Best Practices Checklist for Organizations
To help teams stay aligned, use this quickreference AiTM defense checklist:
✅ All employees enrolled in phishing training that includes AiTM scenarios
✅ WebAuthn/FIDO2 enabled for highrisk roles (finance, admin, IT)
✅ Browser fingerprinting and session token binding enforced
✅ OAuth grant monitoring and revocation tools deployed
✅ Mail flow rules and app passwords audited weekly
✅ All login traffic inspected for TLS JA3 / SNI anomalies
By combining human vigilance with systemlevel defenses, you can stop AiTM phishing before it compromises your business.
Role of AI in Combating AiTM Attacks
Adversary in the Middle phishing attacks have rendered traditional rule based defenses and even some phishing resistant MFA setups increasingly ineffective. In 2026, Artificial Intelligence and Machine Learning have become essential not only for spotting AiTM activity but for automating response before attackers can establish persistence.
In fact, we’ve already seen this play out in SMS phishing campaigns, where AI has helped identify the most spoofed brands by analyzing behavioral patterns at scale.
Leveraging AI and ML for Proactive Defense
AI does more than match indicators of compromise to blacklists. It builds a behavioral fingerprint for every user, device, and session. It understands what a normal login looks like, and flags sessions that deviate from that baseline even if MFA was passed successfully.
In the context of AiTM phishing, AI can:
- Detect when logins originate from known reverse proxy kits or suspicious IP infrastructure
- Flag authenticated sessions that immediately set mailbox rules or perform OAuth grantshallmarks of BEC and persistent access setups
- Correlate email click events with authentication anomalies, especially if a user clicks a link and then passes MFA from a neverbeforeseen browser or geography
These insights are particularly important when protecting users from deepfake enabled pretexting. For more on how AI powered training addresses these threats, explore Keepnet's security awareness training platform.
Future Predictions: What AI Will Do Next
As attackers refine their tactics in 2026, here is what defenders can expect from AI driven security platforms:
- Predictive phishing intelligence: Analyzing emerging domain registrations and phishing kit signals across the dark web to preemptively block infrastructure before it goes active.
- Automated token revocation: Instantly invalidating sessions that trigger AiTM behavioral signals without waiting for SOC analyst intervention.
- Cross platform correlation: Connecting identity signals from Microsoft Entra, Google Workspace, Okta, and EDR tools into a single timeline view.
- Adaptive phishing simulations: Generating AiTM specific training scenarios based on the latest PhaaS techniques observed in the wild.
If your SOC is still relying solely on static detections and playbooks, you are operating with a critical blind spot. Today's AiTM attacks move at machine speed. Integrate AI into every layer of your identity infrastructure now, or risk watching your MFA and awareness investments get bypassed silently.
Further Reading: Explore More Threats and Insights
See the resources below for additional context, case studies, and emerging trends that complement your understanding of AiTM phishing and broader social engineering defenses:
- TelephoneOriented Attack Delivery (TOAD): Learn how TOAD scams exploit voice and urgency to bypass email filters.
- Top 10 Cybersecurity Movies & TV Shows: Get inspired by hacker culture in film and media.
- The Cyber Risk Playbook for Security Leaders: Strategic guidance for CISOs managing evolving threats.
- Phishing vs. Spam Emails: Understand the real difference and how BAS can highlight phishing blind spots.
- The Future of Cyberfraud Fusion: A strategic view on how attackers blend phishing, vishing, and smishing.
- False Clicks in Phishing Simulations: Explore how employee behavior can skew your BAS results and how to fix it.
- Cybersecurity in the Remote Work Era: Importance of cybersecurity for distributed environments.
- The Most Spoofed Brands in SMS Phishing (2025): Understand which brands threat actors impersonate most.
- Language Personalization in Awareness Training: How to improve security culture using nativelanguage BAS content.
- Ransomware Gangs and BlackCat Alpha: Insights into BlackCat Alpha and how to simulate similar extortion tactics safely.
- Security Awareness and Cyber Insurance: How security awareness can reduce premiums and risk exposure for cyber insurance.
- What Is an Information Security Program?: A foundational read before implementing largescale testing.
- Top Cybersecurity Tips for Employees 2025: A companion guide to strengthen human defenses.
- Top Security Projects for 2025 (Gartner Insights): Where BAS ranks among strategic cybersecurity priorities.
- Brand Abuse in Quishing Attacks: How attackers exploit QR codes and logos.
- Preventing DoS Attacks: How to test resilience against denialofservice tactics.
Editor's Note: This article was updated on May 6, 2026.