Top Cybersecurity Practices To Spot Fake Images And Profiles
Fake images and profiles are becoming powerful tools for cybercriminals, fueling phishing, impersonation, and social engineering attacks. In this article, we explore practical cybersecurity practices to help you recognize visual manipulation, spot fake accounts, and safeguard your organization from emerging threats.
Ozan Ucar, Founder and CEO of Keepnet
People all over the world lost $1.3 trillion in 2024 to cyber fraud, according to ExplodingTopics.
Learn more: What Is Security Awareness Training.
The worst thing? This number is expected to grow rapidly in 2025. Australia alone has already lost $76 million in online scams in just the first four months of this year. That's a substantial amount, and it's a sign that cybercriminals are becoming increasingly active day by day.
They use smart ways and rely on advanced technological resources to draw people into their nests. Using fake pictures and fooling people using impersonated identities are among their most common tricks. That's why learning to spot AI or edited photos and fraudulent accounts is now a key step in cybersecurity.
In this article, we will walk you through some of the most effective practices to identify both fake profiles and images. But before that, let's look at the key challenges this problem creates and the trends behind scams run through deceptive accounts and images.
Key Challenges Posed By Fake Images And Profiles
Phony accounts and photographs online are responsible for the following challenges in the internet community:
Threats To Online Security
IC3 reveals that the US received over 860,000 complaints about cybercrimes in 2024, with a huge portion linked to personal data breaches. There could have been many reasons behind this, but there is a higher possibility that a large number may have started with fake accounts.
So, if you are able to recognize them before they engage you in fraud, you can save not just your personal info but also your financial data.
Spread Of Fake News
Edited pictures and stolen identities are among the main sources for spreading falsehoods. With AI tools freely available online, anyone can insert, replace, or manipulate objects to make a completely fake photo. Similarly, creating an account on any social platform is pretty simple. That's what opens doors for fraudsters to share misleading content. But when you spot and report such accounts and pictures on time, you actually stop the further spread of misinformation.
Risk Of Identity Theft
One of the most serious dangers of fake profiles and images is the risk of identity theft. By using fraudulent photos and accounts, they trick people into revealing personal information, which can then be used to impersonate individuals. These new profiles with stolen identities are then used to target the friends and followers of that real person. That's what necessitates verification before interacting with any online account.
Increased Cybercrime Rate
The use of fake profiles and manipulated images is rapidly increasing the overall rate of cybercrimes. For scammers, these are the easiest tools to conduct fraudulent activities like phishing or financial scams. Because it's so simple to create or steal a social account or edit a picture, this ease encourages fraudsters to engage people in fraud on a large scale, which is an alarming threat to your personal security.
Emerging Trends In Fake Images And Profiles Usage
Gone are the days when cybercriminals were limited to traditional tactics of impersonation and image manipulation. Now, they have integrated advanced technology into their scams, making them more powerful than before.
With this advancement, several patterns have become noticeable in how fake pictures and profiles are used in different kinds of fraudulent activities.
Here are the emerging trends in this regard:
Bot-supported account generation: Nowadays, fraudsters don't create every account for cyberattacks manually. Instead, they automated bots that are programmed to create multiple profiles at once with varied names and info. Such accounts don't have any previous history, which makes them easy to identify.
Increased use of AI-made photos: Today, creating a realistic AI photo is easier than editing an existing image. And since AI image generation tools are easily and freely available online, scammers are using this opportunity to create fake pictures for phony accounts. But such photos can also be detected with the right approach.
Platform-specific targeting: Scammers are leaning toward platforms where users are more likely to trust strangers. These especially include Facebook, Instagram, and X (Twitter). Apart from that, reaching out directly into email inboxes has also become a common trend to conduct fraud.
Combined attacks: Many scams are found to be using both fake images and false information together. For example, a fake photo may be paired with a fake story or claim. Cybercriminals usually use this combination to make the deception more believable and harder to detect.
Key Cybersecurity Strategies To Catch Fake Images
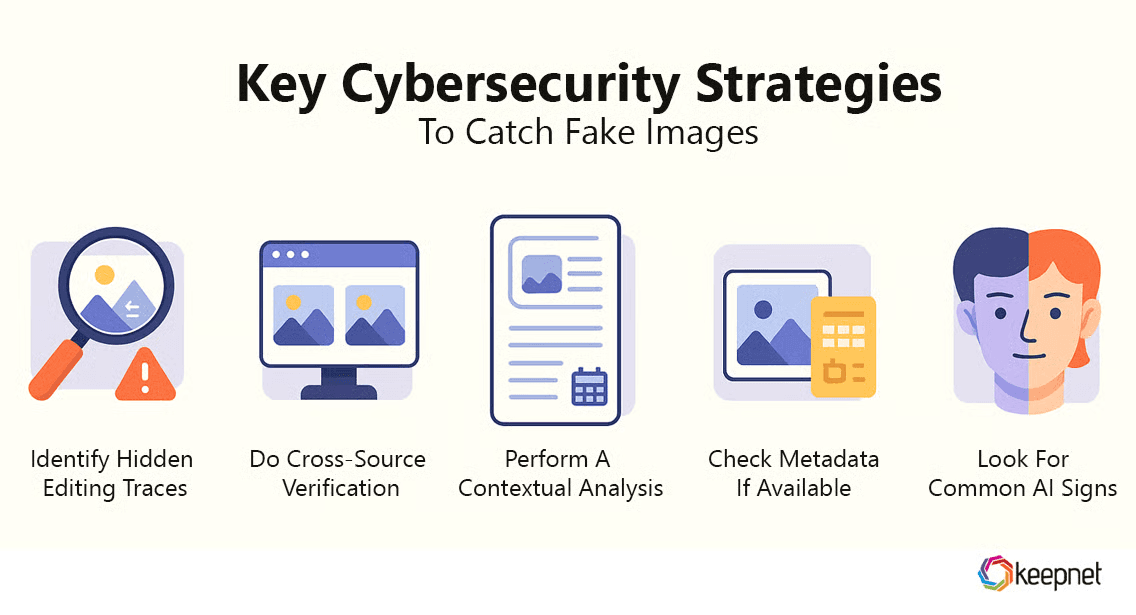
When it comes to identifying if a picture is real or not, you have to perform multiple checks from different aspects. Even cybersecurity professionals use the same techniques when analyzing pictures and accounts.
Let's learn those effective strategies.
Identify Hidden Editing Traces
Whenever an image looks suspicious, check it for subtle traces of editing first. This requires you to perform a deep scan of each part of the photo and look for signs that are not obvious at first glance. These could be
- Rough cutting around the edges of objects.
- Mismatching or missing shadows and reflections.
- Visible clues of background replacement.
- Imbalance or unusual lighting and contrast.
- Excessively blurred parts.
If you notice a couple of these traces, this clearly means that you are looking at a fake image.
Do Cross-Source Verification
Another smart practice to spot fake pictures is to check whether any other credible source has uploaded the same image. To do this, simply search by image, using the photo under observation as your query.
Here’s how you can do it:
- Access an advanced image search tool.
- Upload the sample photo.
- Start the visual search.
The tool will instantly show you all the sources where the same photo appears. Once the matches are displayed, check if the exact version of the image is available on any trusted platform or website. If not, there’s a chance the photo may have been manipulated.
Perform A Contextual Analysis
If the visual analysis doesn't give you enough clues, conduct a contextual examination of that picture. For that, check the context of that photo on the source you first saw it on. Then, go to other sources covering the same image and analyze differences in context.
- Check the publication dates.
- Read the linked story on each source.
- Compare captions and descriptions.
In case you find major discrepancies in the story, date, and other relevant information, that's a clear red flag. All you need is not to fall for that photo, as its context doesn't match reality.
Check Metadata If Available
Checking metadata is also a helpful cybersecurity trick that reveals key information about a picture. BBC, one of the most reliable news outlets, also emphasizes the importance of this practice. Why? Because it answers the following questions regarding an image:
- Who took the image?
- What were the camera settings?
- When was the image taken?
- What software was used to edit it?
- What are the copyright guidelines?
When all these thighs are clear, it becomes pretty easy to validate a picture. But the question is how exactly to check image metadata. Well, for that, the easiest option is to use any freely available EXIF reading tool on the internet.
Look For Common AI Signs
Fake images could not only be edited; they may also be AI-generated. So, in addition to looking for signs of manipulation, it's essential that you also watch out for AI traces. And guess what? Spotting the AI involvement is easier than telling if a photo is altered. Why?
Because AI often leaves more visible mistakes. For instance, an AI picture may have
- Unnatural facial features.
- Distorted hands, fingers, and ears.
- Excessive blurriness on backgrounds.
- Highly perfect settings and skin texture.
- Flawless lighting and contrast.
- Missing or mismatched shadows or reflections.
All such indicators make it obvious that someone has used AI to create that image just to fool others.
Smart Online Security Practices To Spot Fake Profiles
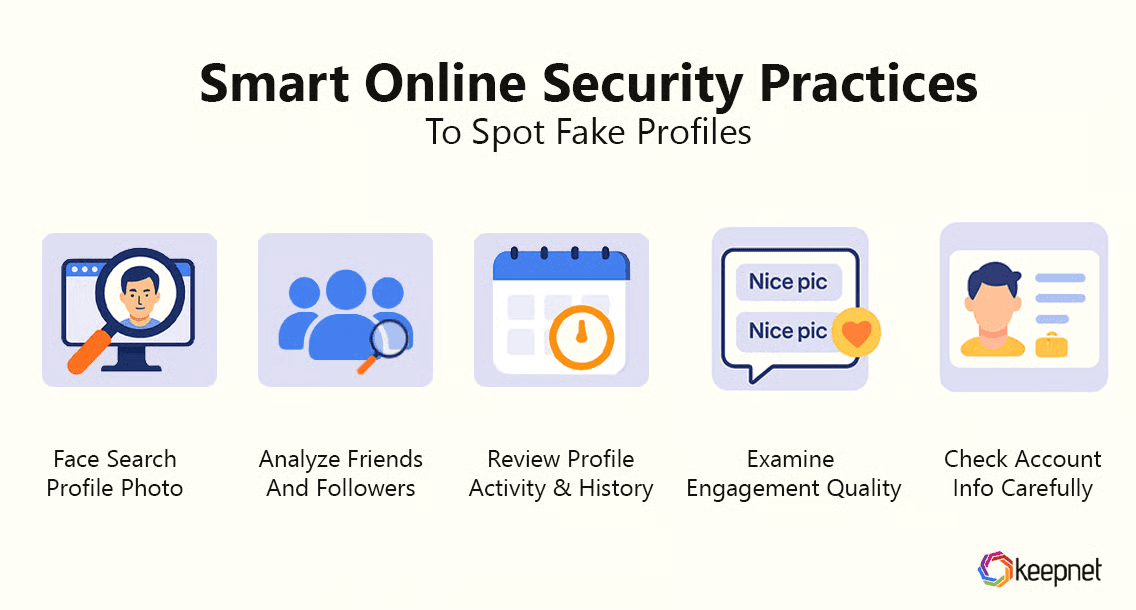
Just like fake images, phony profiles can also be caught, but only if you know the right security practices.
Here are some of the most effective techniques to determine whether a social media account you received a message or friend request from is real or not:
Face Search Profile Photo
The simplest and most efficient way to spot fraudulent social accounts is to run a face search on the profile photo. Fortunately, this technique is incredibly easy, requiring you just
- Save DP of suspicious accounts.
- Go to the face search tool.
- Upload the saved photo there.
- Initiate the search and look into multiple databases.
If the same DP appears on multiple profiles, that's a clear indication that the account is fake.
Analyze Friends And Followers
According to Us.Norton, one of the biggest clues lies in friends and the following list of fake accounts. Such profiles often have an unusual mix of connections. So, if any account seems doubtful,
- See if the listed friends look real and active.
- Check if it has some mutual friends with you.
- Analyze the followers according to the following ratio.
Apart from that, you can also check the friend of their friend for further verification. In case you notice an extreme imbalance, such as thousands of followers with most appearing to be bots, consider it a clear warning sign.
Review Profile Activity & History
Cyabra keeps checking the profile activity among the top steps when it comes to identifying fake profiles. This is because the previous history of a profile can directly hint at whether it has grown naturally over time or not.
Therefore, when analyzing an account,
- See if the account has posted in the same niche so far.
- Look at the post dates and note the posting patterns.
- Check if all the posts were uploaded within a short span.
- Examine if the content matches the profile type.
For instance, if a personal account's post history is filled with unrelated product promotions, it is a strong indicator that the profile may be fake.
Examine Engagement Quality
Another useful practice to authenticate a profile is checking the quality of its engagement. Being a social media user, you might know that genuine accounts receive thoughtful responses from their connections. On the other hand, fake profiles might have a few generic ones. Along with that, they might have
- No comments at all.
- Excessive likes on their posts.
- Too many shares were made through bots.
Together, all such strange patterns in engagement make it clear whether you should trust a profile or not.
Check Account Info Carefully
The details on a profile may contain hidden clues that you can catch by paying close attention. For instance, if someone says they grew up in Toronto, Canada, and studied in Paris, France, but now claims to work in a small business in Lagos, Nigeria, that's a red flag.
So, it's necessary that you closely look at what exactly the profile info tells and if it makes sense.
For that, you can also compare the profile details with their posts. Remember, any major contradiction in the following things could be a direct indication of a phony account.
- Location history
- Education
- Work experience
- Dates and timelines.
How Keepnet Agentic Human Risk Management Helps to Spot Fake Images and Profiles
Keepnet Human Risk Management doesn’t try to be a forensic deepfake detector. Instead, it hardens your people and your workflows so fake photos, AI faces, and impersonator accounts get recognized, reported, and removed fast.
- Train where fakes actually show up: Keepnet runs multi-channel phishing simulations, voice (vishing with AI text-to-speech/voice-clone scenarios), SMS, QR (“quishing”), MFA-fatigue, callback, and email, so teams practice spotting impersonations, doctored visuals, and profile-led scams in realistic contexts (e.g., LinkedIn/job-lure templates).
- Coach with adaptive content: Role-based, adaptive traininguses AI to reinforce cues for fake images/profiles (odd lighting, mismatched eyes/earrings, too-perfect bios, urgency scripts) and to build response habits, especially for HR, help desk, finance, and execs who are prime targets.
- Raise real-time awareness about deepfakes: Keepnet’s guidance and scenarios explicitly cover deepfake-enabled fraud and voice scams, so employees learn how to verify identities before acting.
- One-click reporting from the inbox: When a fake headshot or spoofed profile lands via email, staff can report it with the Phishing Reporter add-in; SOC receives a structured incident automatically.
- Automate triage and takedown: Incident Responderplaybooks analyze reported messages (URLs, files, IPs), auto-investigate, and, based on rules, quarantine or delete malicious mail at scale. This turns “I think this is fake” into measurable, fast action.
- Add breach context to spot impostors: Threat Intelligence flags compromised employee accounts and exposed credentials that attackers often reuse to create convincing fake profiles or executive look-alikes.
- Targeted scenarios for social platforms: Keepnet publishes guidance and runs phishing simulations around LinkedIn and broader social-media scams (fake recruiters, clone brands), helping teams practice verification steps before engaging
Bottom line: Keepnet equips people to recognize visual/manipulation tells, gives them a frictionless way to report, and backs your SOC with automated playbooks, so fakes are spotted sooner and removed faster, without pretending to be a lab-grade image forensics tool.
Editor's Note: This article was updated on March 12, 2026.
What This Means for Teams in 2026
Top Cybersecurity Practices To Spot Fake Images And Profiles is most useful when it helps teams make better day-to-day decisions. The strongest content does more than explain a concept. It shows where risk appears in real work, which actions matter first, and how teams can reduce confusion when the pressure is high.
That is why practical structure matters. A short explanation, a clear response path, and a few repeatable habits usually create more value than broad advice that looks complete but is hard to use.
Keepnet teams usually see stronger results when content like this is tied to a clear workflow, owner, and reporting path. A common mistake is treating top cybersecurity practices to spot fake images and profiles as background knowledge instead of a decision that shows up in real operations.
Keepnet Recommendation
- Translate the concept into a small set of practical decisions users can apply quickly.
- Focus on the workflows where the issue creates the most business exposure.
- Add reporting and escalation guidance so people know what to do under pressure.
- Review the content regularly so examples and priorities stay current.